Security Guide
- About This Guide
- 1 Security and Confidentiality
- I Authentication
- II Local Security
- III Network Security
- IV Confining Privileges with AppArmor
- 18 Introducing AppArmor
- 19 Getting Started
- 20 Immunizing Programs
- 21 Profile Components and Syntax
- 22 AppArmor Profile Repositories
- 23 Building and Managing Profiles with YaST
- 24 Building Profiles from the Command Line
- 25 Profiling Your Web Applications Using ChangeHat
- 26 Confining Users with
pam_apparmor - 27 Managing Profiled Applications
- 28 Support
- 29 AppArmor Glossary
- V SELinux
- VI The Linux Audit Framework
- A GNU Licenses
6 Active Directory Support
Active Directory* (AD) is a directory-service based on LDAP, Kerberos, and other services that is used by Microsoft Windows to manage resources, services, and people. In an MS Windows network, AD provides information about these objects, restricts access to them, and enforces policies. openSUSE® Leap lets you join existing AD domains and integrate your Linux machine into a Windows environment.
6.1 Integrating Linux and AD Environments #
With a Linux client (configured as an Active Directory client) that is joined to an existing Active Directory domain, benefit from various features not available on a pure openSUSE Leap Linux client:
- Browsing Shared Files and Directories with SMB
GNOME Files supports browsing shared resources through SMB.
- Sharing Files and Directories with SMB
Nautilus supports sharing directories and files as in Windows.
- Accessing and Manipulating User Data on the Windows Server
Through Nautilus, users can access their Windows user data and can edit, create, and delete files and directories on the Windows server. Users can access their data without having to enter their password multiple times.
- Offline Authentication
Users can log in and access their local data on the Linux machine even if they are offline or the AD server is unavailable for other reasons.
- Windows Password Change
This port of AD support in Linux enforces corporate password policies stored in Active Directory. The display managers and console support password change messages and accept your input. You can even use the Linux
passwdcommand to set Windows passwords.- Single-Sign-On through Kerberized Applications
Many applications of both desktops are Kerberos-enabled (kerberized), which means they can transparently handle authentication for the user without the need for password reentry at Web servers, proxies, groupware applications, or other locations.
A brief technical background for most of these features is given in the following section. For directions for file and printer sharing, refer to the Book “GNOME User Guide”, where you can learn more about AD enablement.
6.2 Background Information for Linux AD Support #
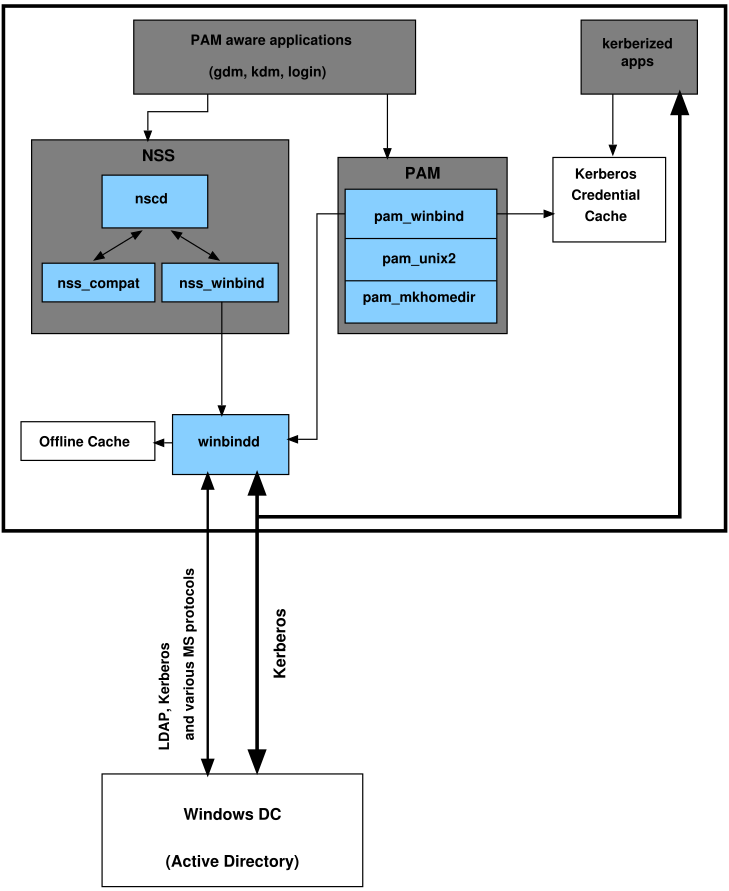
Many system components need to interact flawlessly to integrate a Linux client into an existing Windows Active Directory domain. Figure 6.1, “Active Directory Authentication Schema” highlights the most prominent ones. The following sections focus on the underlying processes of the key events in AD server and client interaction.
Figure 6.1: Active Directory Authentication Schema #
To communicate with the directory service, the client needs to share at least two protocols with the server:
- LDAP
LDAP is a protocol optimized for managing directory information. A Windows domain controller with AD can use the LDAP protocol to exchange directory information with the clients. To learn more about LDAP in general and about the open source port of it, OpenLDAP, refer to Chapter 5, LDAP—A Directory Service.
- Kerberos
Kerberos is a third-party trusted authentication service. All its clients trust Kerberos's authorization of another client's identity, enabling kerberized single-sign-on (SSO) solutions. Windows supports a Kerberos implementation, making Kerberos SSO possible even with Linux clients. To learn more about Kerberos in Linux, refer to Chapter 7, Network Authentication with Kerberos.
The following client components process account and authentication data:
- Winbind
The most central part of this solution is the winbind daemon that is a part of the Samba project and handles all communication with the AD server.
- NSS (Name Service Switch)
NSS routines provide name service information. Naming service for both users and groups is provided by
nss_winbind. This module directly interacts with the winbind daemon.- PAM (Pluggable Authentication Modules)
User authentication for AD users is done by the
pam_winbindmodule. The creation of user homes for the AD users on the Linux client is handled bypam_mkhomedir. Thepam_winbindmodule directly interacts with winbindd. To learn more about PAM in general, refer to Chapter 2, Authentication with PAM.
Applications that are PAM-aware, like the login routines and the GNOME display manager, interact with the PAM and NSS layer to authenticate against the Windows server. Applications supporting Kerberos authentication (such as file managers, Web browsers, or e-mail clients) use the Kerberos credential cache to access user's Kerberos tickets, making them part of the SSO framework.
6.2.1 Domain Join #
During domain join, the server and the client establish a secure relation. On the client, the following tasks need to be performed to join the existing LDAP and Kerberos SSO environment provided by the Window domain controller. The entire join process is handled by the YaST Domain Membership module, which can be run during installation or in the installed system:
The Windows domain controller providing both LDAP and KDC (Key Distribution Center) services is located.
A machine account for the joining client is created in the directory service.
An initial ticket granting ticket (TGT) is obtained for the client and stored in its local Kerberos credential cache. The client needs this TGT to get further tickets allowing it to contact other services, like contacting the directory server for LDAP queries.
NSS and PAM configurations are adjusted to enable the client to authenticate against the domain controller.
During client boot, the winbind daemon is started and retrieves the initial Kerberos ticket for the machine account. winbindd automatically refreshes the machine's ticket to keep it valid. To keep track of the current account policies, winbindd periodically queries the domain controller.
6.2.2 Domain Login and User Homes #
The login manager of GNOME (GDM) has been extended to allow the handling of AD domain login. Users can choose to log in to the primary domain the machine has joined or to one of the trusted domains with which the domain controller of the primary domain has established a trust relationship.
User authentication is mediated by several PAM modules as described
in Section 6.2, “Background Information for Linux AD Support”. The
pam_winbind module used to authenticate clients
against Active Directory or NT4 domains is fully aware of Windows error
conditions that might prohibit a user's login. The Windows error codes
are translated into appropriate user-readable error messages that PAM
gives at login through any of the supported methods (GDM, console, and
SSH):
Password has expiredThe user sees a message stating that the password has expired and needs to be changed. The system prompts for a new password and informs the user if the new password does not comply with corporate password policies (for example the password is too short, too simple, or already in the history). If a user's password change fails, the reason is shown and a new password prompt is given.
Account disabledThe user sees an error message stating that the account has been disabled and to contact the system administrator.
Account locked outThe user sees an error message stating that the account has been locked and to contact the system administrator.
Password has to be changedThe user can log in but receives a warning that the password needs to be changed soon. This warning is sent three days before that password expires. After expiration, the user cannot log in.
Invalid workstationWhen a user is restricted to specific workstations and the current openSUSE Leap machine is not among them, a message appears that this user cannot log in from this workstation.
Invalid logon hoursWhen a user is only allowed to log in during working hours and tries to log in outside working hours, a message informs the user that logging in is not possible at that time.
Account expiredAn administrator can set an expiration time for a specific user account. If that user tries to log in after expiration, the user gets a message that the account has expired and cannot be used to log in.
During a successful authentication, pam_winbind
acquires a ticket granting ticket (TGT) from the Kerberos server of
Active Directory and stores it in the user's credential cache. It also
renews the TGT in the background, requiring no user interaction.
openSUSE Leap supports local home directories for AD users. If configured through YaST as described in Section 6.3, “Configuring a Linux Client for Active Directory”, user homes are created at the first login of a Windows (AD) user into the Linux client. These home directories look and feel entirely the same as standard Linux user home directories and work independently of the AD domain controller. Using a local user home, it is possible to access a user's data on this machine (even when the AD server is disconnected) as long as the Linux client has been configured to perform offline authentication.
6.2.3 Offline Service and Policy Support #
Users in a corporate environment must have the ability to become roaming users (for example, to switch networks or even work disconnected for some time). To enable users to log in to a disconnected machine, extensive caching was integrated into the winbind daemon. The winbind daemon enforces password policies even in the offline state. It tracks the number of failed login attempts and reacts according to the policies configured in Active Directory. Offline support is disabled by default and must be explicitly enabled in the YaST Domain Membership module.
When the domain controller has become unavailable, the user can still access network resources (other than the AD server itself) with valid Kerberos tickets that have been acquired before losing the connection (as in Windows). Password changes cannot be processed unless the domain controller is online. While disconnected from the AD server, a user cannot access any data stored on this server. When a workstation has become disconnected from the network entirely and connects to the corporate network again later, openSUSE Leap acquires a new Kerberos ticket as soon as the user has locked and unlocked the desktop (for example, using a desktop screen saver).
6.3 Configuring a Linux Client for Active Directory #
Before your client can join an AD domain, some adjustments must be made to your network setup to ensure the flawless interaction of client and server.
- DNS
Configure your client machine to use a DNS server that can forward DNS requests to the AD DNS server. Alternatively, configure your machine to use the AD DNS server as the name service data source.
- NTP
To succeed with Kerberos authentication, the client must have its time set accurately. It is highly recommended to use a central NTP time server for this purpose (this can be also the NTP server running on your Active Directory domain controller). If the clock skew between your Linux host and the domain controller exceeds a certain limit, Kerberos authentication fails and the client is logged in using the weaker NTLM (NT LAN Manager) authentication. For more details about using active directory for time synchronization, see Procedure 6.1, “Joining an AD Domain”.
- Firewall
To browse your network neighborhood, either disable the firewall entirely or mark the interface used for browsing as part of the internal zone.
To change the firewall settings on your client, log in as
rootand start the YaST firewall module. Select . Select your network interface from the list of interfaces and click . Select and apply your settings with . Leave the firewall settings with › . To disable the firewall, check the option, and leave the firewall module with › .- AD Account
You cannot log in to an AD domain unless the AD administrator has provided you with a valid user account for that domain. Use the AD user name and password to log in to the AD domain from your Linux client.
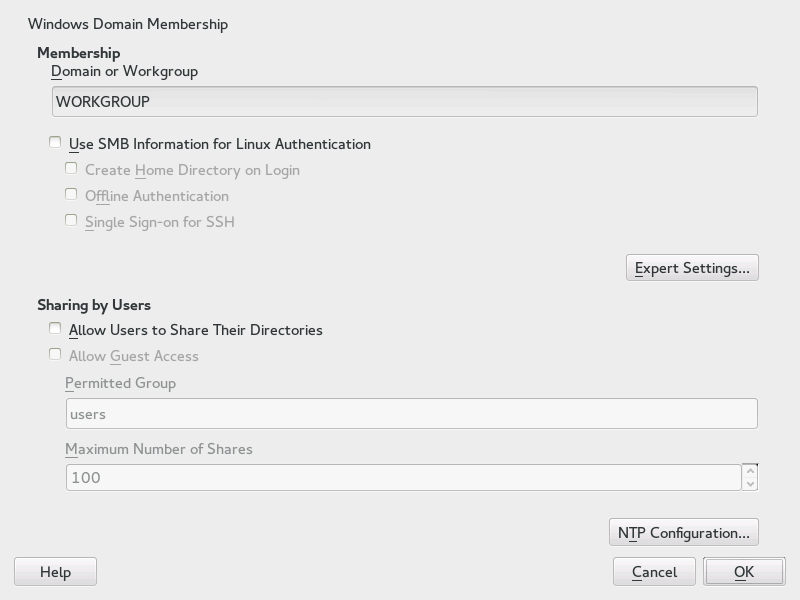
To join an AD domain, proceed as follows:
Procedure 6.1: Joining an AD Domain #
Log in as
rootand start YaST.Start › .
Enter the domain to join at in the screen (see Figure 6.2, “Determining Windows Domain Membership”). If the DNS settings on your host are properly integrated with the Windows DNS server, enter the AD domain name in its DNS format (
mydomain.mycompany.com). If you enter the short name of your domain (also known as the pre–Windows 2000 domain name), YaST must rely on NetBIOS name resolution instead of DNS to find the correct domain controller.Figure 6.2: Determining Windows Domain Membership #
Check to use the SMB source for Linux authentication.
Check to automatically create a local home directory for your AD user on the Linux machine.
Check to allow your domain users to log in even if the AD server is temporarily unavailable, or if you do not have a network connection.
Select , if you want to change the UID and GID ranges for the Samba users and groups. Let DHCP retrieve the WINS server only if you need it. This is the case when some machines are resolved only by the WINS system.
Configure NTP time synchronization for your AD environment by selecting and entering an appropriate server name or IP address. This step is obsolete if you have already entered the appropriate settings in the stand-alone YaST NTP configuration module.
Click and confirm the domain join when prompted for it.
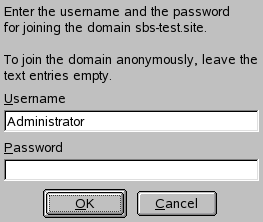
Provide the password for the Windows administrator on the AD server and click (see Figure 6.3, “Providing Administrator Credentials”).
Figure 6.3: Providing Administrator Credentials #
After you have joined the AD domain, you can log in to it from your workstation using the display manager of your desktop or the console.
Important: Domain Name
Joining a domain may not succeed if the domain name ends with
.local. Names ending in .local
cause conflicts with Multicast DNS (MDNS) where
.local is reserved for link-local host names.
Note
Currently only a domain administrator account, such as
Administrator, can join openSUSE Leap into Active
Directory.
6.4 Logging In to an AD Domain #
Provided your machine has been configured to authenticate against Active Directory and you have a valid Windows user identity, you can log in to your machine using the AD credentials. Login is supported for GNOME, the console, SSH, and any other PAM-aware application.
Important: Offline Authentication
openSUSE Leap supports offline authentication, allowing you to log in to your client machine even when it is offline. See Section 6.2.3, “Offline Service and Policy Support” for details.
6.4.1 GDM #
To authenticate a GNOME client machine against an AD server, proceed as follows:
Enter the domain name and the Windows user name in the form of Domain_Name\Windows_User_Name in the field and press Enter.
Enter your Windows password and press Enter.
If configured to do so, openSUSE Leap creates a user home directory on the local machine on the first login of each AD authenticated user. This allows you to benefit from the AD support of openSUSE Leap while still having a fully functional Linux machine at your disposal.
6.4.2 Console Login #
Besides logging in to the AD client machine using a graphical front-end, you can log in using the text-based console or even remotely using SSH.
To log in to your AD client from a console, enter
DOMAIN\user
at the login: prompt and provide the password.
To remotely log in to your AD client machine using SSH, proceed as follows:
At the login prompt, enter:
ssh DOMAIN\\user@host_name
The
\domain and login delimiter is escaped with another\sign.Provide the user's password.
6.5 Changing Passwords #
openSUSE Leap has the ability to help a user choose a suitable new password that meets the corporate security policy. The underlying PAM module retrieves the current password policy settings from the domain controller, informing the user about the specific password quality requirements a user account typically has by means of a message on login. Like its Windows counterpart, openSUSE Leap presents a message describing:
Password history settings
Minimum password length requirements
Minimum password age
Password complexity
The password change process cannot succeed unless all requirements have been successfully met. Feedback about the password status is given both through the display managers and the console.
GDM provides feedback about password expiration and the prompt for new passwords in an interactive mode. To change passwords in the display managers, provide the password information when prompted.
To change your Windows password, you can use the standard Linux utility,
passwd, instead of having to manipulate this data on
the server. To change your Windows password, proceed as follows:
Log in at the console.
Enter
passwd.Enter your current password when prompted.
Enter the new password.
Reenter the new password for confirmation. If your new password does not comply with the policies on the Windows server, this feedback is given to you and you are prompted for another password.
To change your Windows password from the GNOME desktop, proceed as follows:
Click the icon on the left edge of the panel.
Select .
From the section, select › .
Enter your old password.
Enter and confirm the new password.
Leave the dialog with to apply your settings.